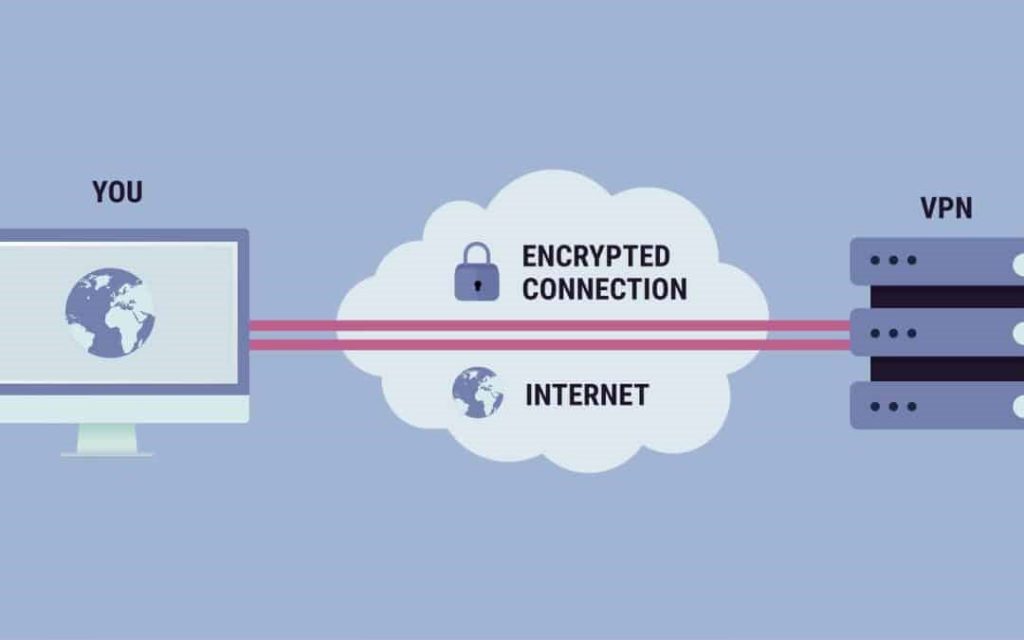
A VPN is defined as a “Virtual Private Network” and it describes the ability to provide a secure connection when you use an open network. A VPN encrypts all your internet traffic and hides your identity online. This will make it more difficult for them to track your online activities and steal your information. Data encryption takes place in real-time.
VPN: How Does Its Work?
A VPN can hide your IP address on your network, which will enable you to associate it with a specific remote control, VPN, hosting the management server. This means, that if you are browsing on the Internet, with the help of a VPN, the VPN server will be a source of information. This means that an Internet Service Provider (ISP), and any third party, not knowing what websites you visit or what data to send and buy online. The VPN acts like a filter to get all of the data in the “mumbo jumbo language and turned himself in. Also, if someone gets ahold of the information that there is going to be useless.
VPN: What Are The Benefits Of The Connection?
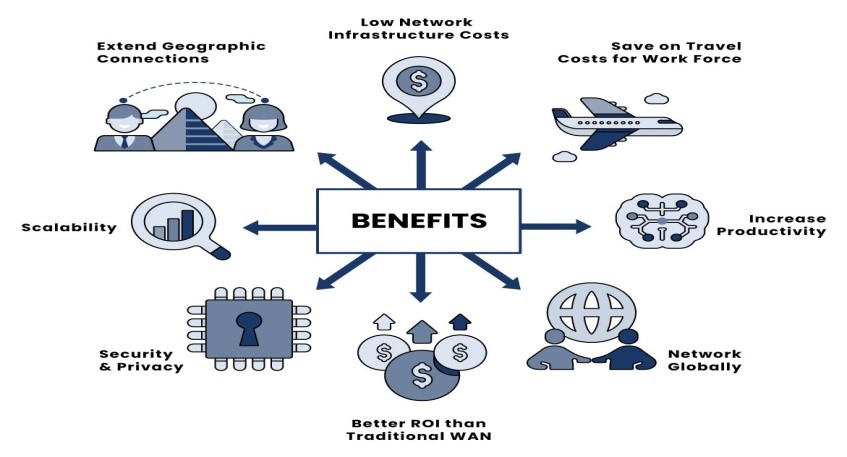
A virtual private network images on your Internet traffic data and protects it from the external input terminal. Unencrypted data can be used by anyone who has access to your network and wants to see it. By using a VPN, hackers, and won’t be able to decrypt the data.
Secure Encryption: To read the data, you will need the encryption key. But the computer would have taken millions of years to understand the code, in the case of a “brute-force” attack. With a VPN your internet activity is going to remain a secret, even in the open network.
- Disguising Your Where Aboutsz: the VPN server is functioning as a proxy server on the Internet. As the information on your demographic location to be sent to the server in another country, and your actual location can’t be determined. In addition, most VPN services do not store logs of your actions. Some suppliers, on the contrary, a record of your behavior, but to pass on this information to any third party. This means that any record of your behavior is permanently hidden.
- Access to Regional Content: the Regional content on the web is not always available at all locations. The services and the sites frequently contain content that is not available in all regions of the world. The standard, to connect and use local servers in the country, to the site’s determination. This means that you can download the content, at home, while traveling, and you can get free content at home. By using a VPN function of the website, you can go to a server in another country and is an effective way to “change” your position is.
- Secure Data Transfer: If you’re working remotely, you may need to have access to the files on your business network. For security reasons, this information in a safe and secure connection. A virtual private network connection, which is often required to access the network. The VPN service to connect to your server, and the use of encryption technology to reduce the risk of information leakage.
VPN: Why Should You Use The Connection?

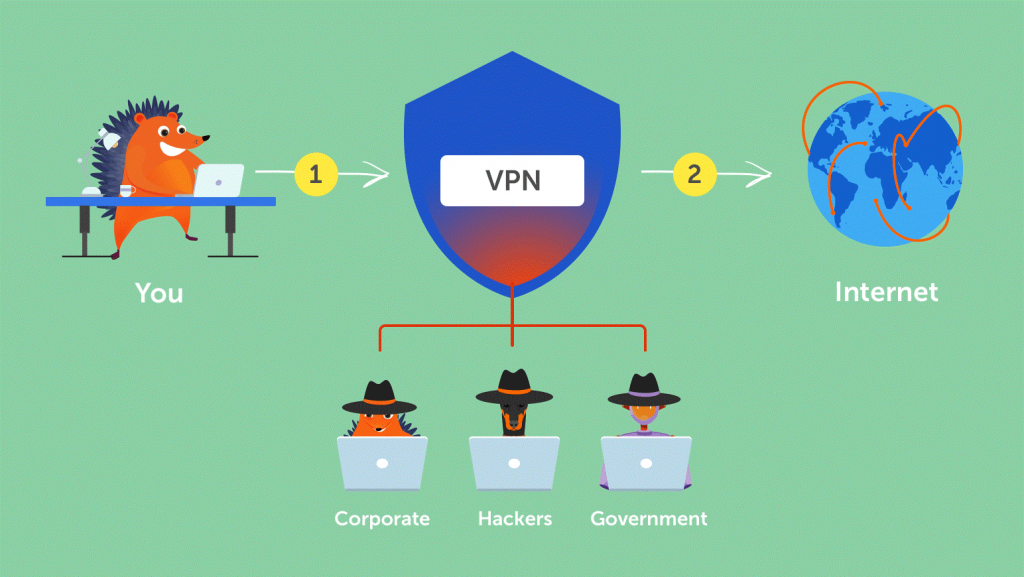
Your internet provider is usually set up when you have internet. The track you through IP address. Your network traffic will be routed through the provider’s servers, which can record and check to make sure everything you do is online.
, Your Internet service provider (isp may appear trustworthy, but it can be also to share the story of advertisers to the police, or government, and/or other third parties. Internet service providers (ISPs may also be the victim of attacks by cybercriminals if they are hacked, their data and personal data could be at risk.
This is especially important if you regularly connect to an open Wi-Fi network. You never know who can direct your Internet traffic, and might be what you are stealing, including the passwords, and personal information of the payment, or even the whole of the person.
Standard VPN: What Should It Do?

STANDARD
VPN
What Should It Do?
You can be confident in your VPN implementation, one or more of the tasks. VPNs ought to be protected from compromise. In particular, this is to be expected from a comprehensive VPN solution:
- Encrypt Your Internet Protocol Address: The main function of a VPN is to hide the IP address from your internet provider, and other third parties, This way you can send and receive information over the Internet, but the risk is no more than that, you and the VPN provider will have to look at it.
- Encryption Protocols: VPNs, and should also prevent you from keeping track of the mind, for example, your Internet history, browsing history, etc, the Encryption is particularly important, as it prevents the third party from gaining access to sensitive information like personal information, financial information, and other site materials.
- Kill Switch: If your VPN connection is suddenly interrupted, your safe contacts list will also get in the way. It is the best VPN to find out that this was an unexpected downtime and at the end of the selected program, which will decrease the likelihood that the information will be put at risk.
- Two-Factor Authentication: Two-factor authentication using different authentication methods provides a powerful VPN for controls, all of which are trying to log in. For example, it might be something for you to enter your password and then a code will be sent to your mobile phone. This makes it difficult for uninvited third parties to have access to your secure connection.
A DAY IN THE LIFE OF A VPNs

As people began to make use of the Internet, there has been a movement to protect and encrypt the web browser of the data. The united states department of Defense has already been involved in projects to encrypt information on the Internet, communications of the 1960s.
The Predecessors Of The VPN
Their efforts led to the creation of the ARPANET (the Advanced Research Projects Agency Network, a packet-switched network, which, in turn, led to the development of a transmission control protocol/Internet protocol (TCP/IP).
The TCP / IP four-layer Communication, Internet, Transport, and Application. At the level of the Internet, a local area network and can connect to a public network, and this is where the risk of exposure is clear. In 1993, a team from Columbia University and AT&T’s Bell Labs has finally been able to create a shape out of the first version of a modern VPN, which is called the Sweep-IP-encryption-protocol software.
In the following year, by Xu Wei, the developed protocol security (IPSec) network, the Internet, the security protocol that authenticates and encrypts all of the information packages, to share the Internet connection. In 1996, a Microsoft employee named Gurdeep Singh Pall created a peer-to-Peer Tunneling Protocol (PPTP).
At The Beginning Of The VPNs In parallel with the development of the PPTP, Singh Pall has increased the popularity of the Internet, and there is a need for a consumer-ready, integrated safety management system. This is when the anti-virus program is already to be effective in the prevention of malware and spyware from infecting your computer. However, people and companies have begun to require the encryption of software, to be able to cover their travel and online dating.
Thus, the first of the VPN is turned up at the beginning of the year 2000, however, we can say that it is only used in the business. However, after a stream of a breach of security, and in particular at the beginning of the 2010s, the end-user of the VPN service of the market began to grow.
VPNs And Their Current Use

According to GlobalWebIndex, the number of VPN users all over the world, with more than quadrupled between 2016 and 2018. That is, in countries such as Thailand, Indonesia, and China, where Internet usage is restricted and subject to censorship, where one out of every five Internet users uses a virtual private network. In the united states, the united kingdom, and Germany, the share of the VPN, the user is low (about 5%), but it’s growing.
One of the main driving forces for the use of a Vpn in the past few years has been the growing demand for content with geographic restrictions. For example, streaming services such as Netflix and YouTube, to define, this video is only available in certain countries. With the help of a modern Vpn, you can encrypt your IP address, so that it looks like you are visiting, and to other countries so that you can get this content anywhere in the world.
VPN And How To Surf Securely With It
A VPN encrypts all of your browsing habits in order as there can only be decrypted using a key. Only a personal computer and a VPN are to know that this is the key so that your ISP can see that it is there, you are on the web. Variety of virtual private network (Vpn uses a variety of techniques for encryption, but usually it works in three steps:
- Once you are online, start your VPN. The VPN acts as a secure tunnel between you and the internet. Your ISP and other third parties cannot detect this tunnel.
- Your device is now on the local network of the VPN, and your IP address can be changed to an IP address provided by the VPN server.
- Now you can surf the Internet on the basis that, a VPN protects all your data.
Types of VPNs
There are a lot of different types of VPNs, but you should certainly be familiar with the three main types of VPN:
SSL VPN
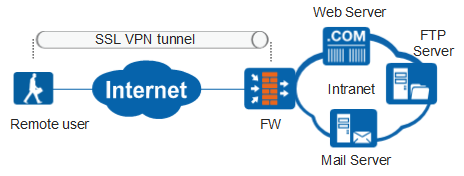
The website of a VPN is, in essence, a private network, which is designed to hide private intranets and allows users to secure the network, to gain access to each other’s resources.
Vpn access to the ‘website’ type is also useful if you have multiple locations for your business, each of which has its Local area Network (LAN) is connected to the Wide Area Network (WAN). A site-to-site VPN is also useful when you have two separate intranets, and among them, you’ll want to send this file to make it clear to other users ‘ intranet zone.
A site-to-site VPN is used primarily in large corporations. The most difficult of the exercises, and do not offer the same level of comfort as the SSL-VPN. However, they are the most efficient and effective method to ensure communication between and within teams.
Site-To-Site VPN
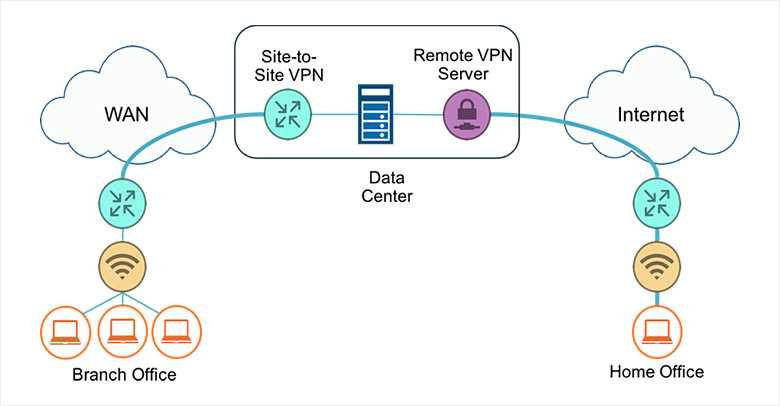
The website of a VPN is, in essence, a private network, which is designed to hide private intranets and allows users to secure the network, to gain access to each other’s resources.
Vpn access to the ‘website’ type is also useful if you have multiple locations for your business, each of which has its Local area Network (LAN) is connected to the Wide Area Network (WAN). A site-to-site VPN is also useful when you have two separate intranets, and among them, you’ll want to send this file to make it clear to other users ‘ intranet zone.
A site-to-site VPN is used primarily in large corporations. The most difficult of the exercises, and do not offer the same level of comfort as the SSL-VPN. However, they are the most efficient and effective method to ensure communication between and within teams.
Client-To-Server VPN
Connecting via a VPN, the client may think that if you could connect your computer to a company that the use of an extension cord. Employees connect to the company network, from home too, office, over a secure connection and act like them when you are sitting in your office. But first, the VPN client software must be installed and to be installed on the computer.
This means that the user can connect to the Internet through their internet service PROVIDER, and identify and communicate directly through the VPN service provider. This greatly reduces the tunnel, the speed of a VPN for travel. Instead of using a VPN for encryption, the encryption makes the data available for the connection to the Internet, a VPN can automatically encrypt data before it is made available to the user.
This is the most common type of VPN, which is especially useful, and dangerous to an open NETWORK. It prevents third-party access to the network for the connection, and the trade-offs, and also encrypts the data up to the service provider itself. It also prohibits Internet service providers from being paid for something that, for whatever reason, they are still uncertain and circumvent any user limits on the Internet (for example, if a country’s government restricts Internet access.
The advantage of this type of VPN to all the effectiveness and versatility, to which the company will receive. If there is a suitable phone system is available, an employee may, for example, connect to the system with the help of the headphones to act as if they are in the workplace and their business
Steps Of Installing A VPN On A Computer

Before installing a VPN, it is important to know the different implementation methods:
VPN Client
The program should be defined for a flight, the VPN client. With this software, install following the requirements set out in the last paragraph. Once you’re set up with a VPN, to the point that the carrying out of a VPN connection, connecting, on the other hand, at the last possible moment, to generate the encryption tunnels. In business, this is the stage that would require you to type in the password provided by the company or, to install the appropriate certificate. Through the use of a password or a certificate, the firewall may see this as an approved connection. The employee is then to identify it as a known point of reference.
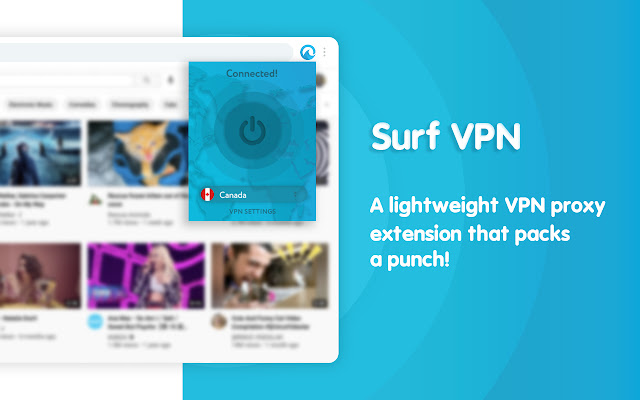
Browser Extensions
With the VPN extension, you can add them to the majority of web browsers such as Google Chrome, and Firefox. Some browsers, including Opera, also have their VPN integration of the add-ons. The add-in will make it easier for users to rapidly change and put up their virtual private network (VPN when they are browsing on the internet. However, the VPN connection is that is just for your information, this is the web browser. The use of any other internet browser and the other is the use of the Internet, outside of the browser (for example, the online game): it can be encrypted by the VPN.
Also, if the browser add-ons, as strong as a VPN client, that may be the case that they are suitable for a selection of the casual Internet user who needs an extra layer of security online. However, they have become more susceptible to crime. Users are also encouraged to choose an influential extension of the collector can try to use the wrong VPN in add-ons. The collection of Data collection of personal data, which the marketer can do, is to create your profile. Then, the advertisement content is chosen for you.
Router VPN
If you have multiple devices connected to the same Internet connection, it may be easier to implement with a VPN directly to the router, other than to set it up for Vpn access on any device. A VPN router is particularly useful if you want to protect your devices with an Internet connection, which is hard to be set up, such as the smart Tv. They will also help you to get the geographically restricted content on your home entertainment system.
The VPN router is an easy-to-install, always provides security and confidentiality, and also prevent dangerous products from compromise the network, when you are logged in. But it can be hard to deal with if your router has its user interface. This can result in new connections will be blocked.
Company VPN
The company’s VPN, tailored solutions, which require separate installation, and technical support. A VPN is usually made of the company’s BUSINESS of the group. As a user, you are not administratively affected by most of the VPN, all your activities, and the transfer of the data is registered to your company. This allows the company to minimize the potential risk of information leakage. The main advantage of using a VPN is a completely safe and secure connection to the intranet, and the company’s server, though for employees who work outside the company to use its internet connection.
Can VPN Also Work On Smartphone Or Other Devices?

Yes, there are several VPN options are available to smartphones and other Internet-connected devices. A virtual private network (VPN may be required for your mobile device, and if you’re using it for is to store the information of the payment or any other personal information that you, or just surf on the internet. Many VPN service providers offer mobile solutions, many of which can be downloaded directly from the Google Play or Apple App Store on your device.
Is VPN Secure?

It is important to note that the VPN connection is not working as a comprehensive antivirus software program. Also, if they are to protect your IP address and encrypt your Internet history, with a virtual private network to protect your computer system from outside interference. To do this, you will need to use anti-virus software. Therefore, with the help of a VPN is not in and of itself, to protect you from Trojans, viruses, bots, or other harmful components.
Then, the malicious code will be entered into the device, which can steal or damage data, regardless of whether you are using a VPN or not. That is why it is important to use a VPN in conjunction with a comprehensive anti-virus application for maximum security.
Selecting a secure VPN provider It is also important to choose a VPN service provider that you can rely on and trust. But your ISP might not be your internet traffic, a VPN provider can be. If your VPN provider benefits, it’s when you do it. For this reason, you must select a reliable VPN provider to see how it is to hide your internet activity and to ensure the highest level of security
Step Of Installing A VPN Connection On A Smartphone
As mentioned before, there is a virtual private network for both Android and iPhone smartphones. Fortunately, VPN services, who is in the smartphones, easy to use, and is common as it is in:
- Advanced setup is available for users requiring a higher degree of data protection. Depending on your VPN, you can also select other protocols for your encryption method. Diagnostics and other functions may also be available in your app. Before you subscribe, learn about these features to find the right VPN for your needs.
- The installation process usually only downloads one app from the iOS App Store or Google Play Store. Although free VPN providers exist, it’s wise to choose a professional provider when it comes to security.
- To surf the internet safely from now on, all you have to do is first activate the VPN connection through the app.
- The setup is extremely user-friendly, as the default settings are already mostly designed for the average smartphone user. Simply log in with your account. Most apps will then guide you through the key functions of the VPN services.
- Switching on the VPN works like a light switch for many VPN apps. You will probably find the option directly on the home screen.
- Server switching is usually done manually if you want to fake your location. Simply select the desired country from the offer.
But keep the following in mind: A VPN is safe, as is the data on use, and retention policies to their provider. Keep in mind that the VPN is a service that allows you to have your server, and the server connects over the Internet on your behalf. If they are storing the data in the log, make sure that it is clear for what purposes these logs will be stored. The grave of the VPN providers tends to put privacy first. Therefore, it is necessary to choose a reliable service provider.
Please note that there is access to the Internet, and the transfer of the data to be encrypted. Anything that does not use a network connection or Wi-Fi internet access is going to be transmitted over the Internet. As a result, your VPN does not encrypt your regular voice calls and text messages.
Conclusion

A VPN connection provides a secure connection between you and the Internet. For a VPN, your traffic is sent through encrypted virtual tunnels. There are also pictures of your IP address when you use the internet, which makes its location, hidden from everyone. The VPN connection, the defense, the offense. This is because only you can get access to the information in a secure encrypted tunnel and that no one else can, because they don’t have the key. A VPN will give you access to local and restricted content anywhere in the world. Many of the streaming platforms are not available in every country. You can still get them is to use a VPN.
At present, there are also many of the smartphone’s virtual private network providers to maintain the privacy of the mobile data traffic. You can find out on the authorized dealers can be found in the Google Play Store or iOS App Store. However, keep in mind that it is not only your Web traffic that is aggregated and therefore anonymous and protected with VPN. A VPN also protects you from hacker attacks, Trojans, viruses, and any other malware, malicious code on it. Therefore, you will need to just rely on reliable anti-virus software.
Finally, to make use of a legitimate VPN provider. Be careful free of charge. Soon, a lot of people abroad will be defining a free VPN for Nigerians. Please, let’s take a closer look before you leap in. Along with this, in the case of the 419th and fraud may also explode if damaged.




